- Cisco Anyconnect Secure Mobility Client Free
- Anyconnect Ad Authentication Manager
- Anyconnect Ad Authentication Failed
- Anyconnect Ad Authentication App
- Anyconnect Ad Authentication Failed
Using Active Directory as a LDAP server with ASA For a long time the only way to use Active Directory (AD) for VPN authentication and authorization was to use a RADIUS server such as Cisco ACS that.
I would like to share my experience with VPN Remote Access and Multi Factor Authentication with products from Cisco and Duo Security:
See full list on petenetlive.com. Cisco AnyConnect, AD/Radius authentication, multiple group policies 3 posts geronimo1000. Ars Centurion Registered: Jan 27, 2003. Posted: Thu Apr 08, 2010 4:46 pm.
- Cisco Identity Services Engine 2.X,
- Cisco ASA 5500-X
- Anyconnect Secure Mobility Client (VPN client)
- MFA Cloud based services from Duo Security
Background of Multi Factor Authentication
Multi Factor Authentication (MFA) is already quite well known approach in achieving more secure authentication process. The aim of this type of authentication is to provide additional level of security ensuring that authenticating user proves his identity with different factors, independent from each other. The MFA paradigm is that the user proves his identity by providing information that he knows (example: user credentials) and then providing information based on what he owns (example: hardware or software token). This procedure increases the probability of genuine authentication and make sure it is not fake. In a hypothetical scenario an attacker can steal user credentials by spying, sniffing or guessing if password is not secure enough, but when using MFA the use of another factor makes such attack more difficult because the attacker does not possesses the second factor for authentication. The second (or third) factor can be of different kinds for instance physical, application based, connected or standalone. They could be a physical or logical tokens, phone calls, text messages or push messages.
How does second factor authentication work?
Rang amjad sabri mp3 download. Lets quickly introduce popular types of different authentication factors.
Credentials
The most popular – users knows their username and passwords and provide them while authenticating.
Certificates
Also a popular factor – users have enrolled with their personal certificates and uses X509 framework to authenticate. If you want to know about the certificate authentication process in detail have a look at ITU standards here.
Tokens
Token provides one-time password that changes in fixed time intervals, for example every 60 seconds. One-time password (OTP) is displayed with synchronization with reference server often known as token server. Synchronization is done between token internal clock and token server clock. Both parties generate pseudo random number thanks to OATH algorithm or any variation of OTP generation algorithm. Tokens can be hardware (i.e. RSA SecureID hardware) or software based (i.e. mobile apps for iOS or Android). The downside of the hw tokens is that they are expensive in implementation.
Cerb Software token MFA example
Push notifications
Good choice for big implementations (often cheaper than hardware tokens) is push notification method where User is prompted actively by mobile App to Approve or Decline the fact of authentication. This method is used in conjunction with smartphone device and installed mobile app on it. This kind of authentication factor is used in our case study.
The Hook Up free download - What's Up, Sudoku Up 2020, Pop Up Blocker Pro Rich Media Ads Edition, and many more programs. Click on 'Download Pure, the hookup app APK' link to start downloading the apk file on your PC. How to Download Pure, the hookup app for PC or MAC: Initially, you have to free download either BlueStacks or Andy os to your PC using free download link displayed within the starting on this web site.  The Hook-Up by - view all games by author Category: Flash: Adventure Average Play: 15 / 14655 (per day / total) Average Rating: None A game of charm, treachery, and deceit. Play your cards right and you might even find love, virtual style. Submitted on 12/2/07.
The Hook-Up by - view all games by author Category: Flash: Adventure Average Play: 15 / 14655 (per day / total) Average Rating: None A game of charm, treachery, and deceit. Play your cards right and you might even find love, virtual style. Submitted on 12/2/07.
SMS Passcodes
Another type of factor is sending SMS code which needs to be provided by user during authentication prompt. This requires SMS gateway for that process.
Callback phone
Some of market solutions enable “callback phone’ that is automaticaly processed after first factor is correctly passed. After phone call, user is able to press required key. This method works well for offline users for example those who do not use the smartphones.
The project aim and chosen solution
The aim was to increase a security level for User VPN authentications. Customer had Cisco infrastructure with high level of integration. After business needs analysis and infra assessment and then several days of Proof of Concept project the choice was Duo Security product for MFA solution because of its flexibility and user friendly interface. There were also signs that it will smoothly integrate within the Cisco architecture components.
Architecture components and authentication flow
The steps of authentication is as follows:
- User connects with Anyconnect Secure Mobility Client to ASA Headend
- User is prompted to provide Domain credentials
- Credentials are sent to VPN Headend encrypted
- ASA VPN checks credentials with Duo AuthProxy then Duo with ISE. Both communication via Radius.
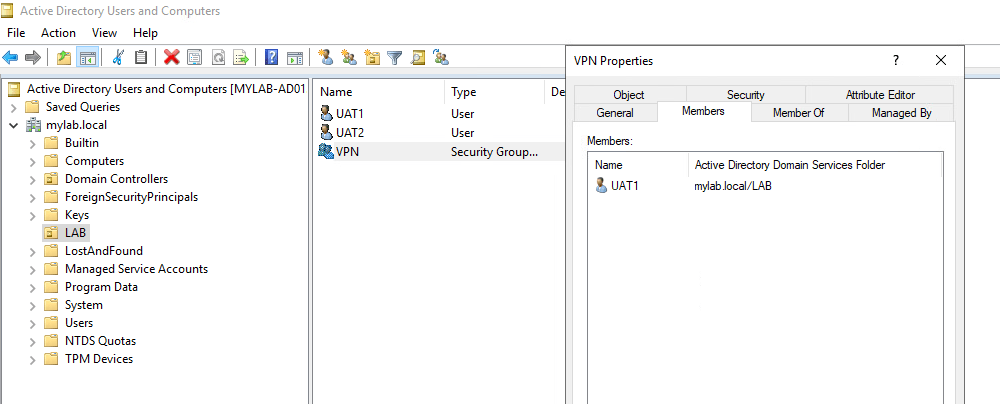
- Cisco ISE in turn verifies user and password with AD Controller
- AD responds to ISE. If fails ISE sends the Radius Reject packet back to Duo and then Duo to ASA
- If succeeded Duo sends the request with username to Duo Cloud
- Duo Cloud then pushes the Approve / Deny message to Mobile App of authenticating user
- User accepts (or denies) the connection. If denies, the Radius Access Reject is send via Duo AuthProxy to ASA and connection is torn down.
- After Accept from Mobile information is going back to Cloud and then to AuthProxy and finally is landing on ASA VPN Headend
- ASA establishes VPN connection with Anyconnect
- Last but not least, the accounting message that confirms the established session is sent from ASA to ISE for logging and accounting purposes (piggybacking IP address, Username, Timestamp and more)
Traffic flow high level view – MFA authentication
VPN Multi Factor Authentication idea traffic flow
ASA VPN Headend
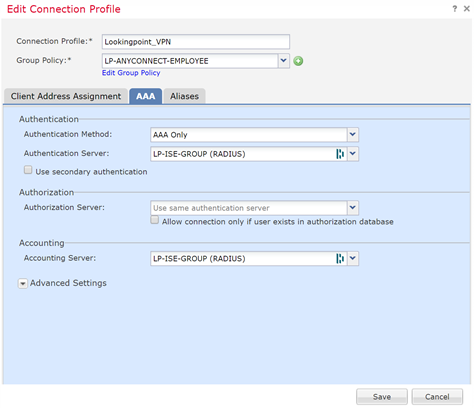
The ASA configuration part is very similar to regular remote access implementation with Cisco Anyconnect. One thing to mention is accounting and authentication server part. In our case study ASA acts as a radius client to Duo Authentication Proxy and in parallel to ISE Policy Service Nodes. The Duo Authentication Proxy in turn is the proxy between ASA, ISE PSN and Duo Cloud API.
Cisco ISE part
Besides regular Authentication and Authorization rules Duo Auth Proxy need to be configured as a radius client on Cisco ISE. Cisco ISE acts as:
- Radius Server for Duo Auth Proxy
- Radius Server for ASA VPN
- Proxy for AD authentication
ISE functions in our case study:
- Authentication Server (AD as external identity source)
- Authorization Server for differentiate Users and Groups access privileges
- Accounting Server for log storage and User-to-IP mapping source
In this project User-to-IP mappings are crucial for whole infrastructure because these mappings are used in different segments for identity access. The purpose of identity filtering is described here.
Duo Authentication Proxy
Duo Auth Proxy can be hosted on Linux or Windows Server machine. Duo Authentication proxy is the interface between ISE and ASA, ASA and Cloud API, ISE and Cloud API. You can take a look at the config guides at Duo site https://duo.com/docs/authproxy_reference
Duo Cloud and Active Directory
For the sake of proper authentication, user and mobile devices handling, the Duo Cloud interface is used. There is connection established between Duo Auth Proxy, Duo Cloud API and Active Directory that is used for AD authentication, user and device enrolment with Duo Mobile App.
The solution was integrated with high-availability environment and there is no single point of failure within the VPN infrastructure. For further details of components and their configuration, follow us on Grandmetric LinkedIn site
-->
In this tutorial, you'll learn how to integrate Cisco AnyConnect with Azure Active Directory (Azure AD). When you integrate Cisco AnyConnect with Azure AD, you can:
- Control in Azure AD who has access to Cisco AnyConnect.
- Enable your users to be automatically signed-in to Cisco AnyConnect with their Azure AD accounts.
- Manage your accounts in one central location - the Azure portal.
Prerequisites
Cisco Anyconnect Secure Mobility Client Free
To get started, you need the following items:
- An Azure AD subscription. If you don't have a subscription, you can get a free account.
- Cisco AnyConnect single sign-on (SSO) enabled subscription.
Scenario description
Anyconnect Ad Authentication Manager
In this tutorial, you configure and test Azure AD SSO in a test environment.
- Cisco AnyConnect supports IDP initiated SSO
Adding Cisco AnyConnect from the gallery
To configure the integration of Cisco AnyConnect into Azure AD, you need to add Cisco AnyConnect from the gallery to your list of managed SaaS apps.
- Sign in to the Azure portal using either a work or school account, or a personal Microsoft account.
- On the left navigation pane, select the Azure Active Directory service.
- Navigate to Enterprise Applications and then select All Applications.
- To add new application, select New application.
- In the Add from the gallery section, type Cisco AnyConnect in the search box.
- Select Cisco AnyConnect from results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Configure and test Azure AD SSO for Cisco AnyConnect
Configure and test Azure AD SSO with Cisco AnyConnect using a test user called B.Simon. For SSO to work, you need to establish a link relationship between an Azure AD user and the related user in Cisco AnyConnect.
To configure and test Azure AD SSO with Cisco AnyConnect, perform the following steps:
- Configure Azure AD SSO - to enable your users to use this feature.
- Create an Azure AD test user - to test Azure AD single sign-on with B.Simon.
- Assign the Azure AD test user - to enable B.Simon to use Azure AD single sign-on.
- Configure Cisco AnyConnect SSO - to configure the single sign-on settings on application side.
- Create Cisco AnyConnect test user - to have a counterpart of B.Simon in Cisco AnyConnect that is linked to the Azure AD representation of user.
- Test SSO - to verify whether the configuration works.
Configure Azure AD SSO
Follow these steps to enable Azure AD SSO in the Azure portal.
In the Azure portal, on the Cisco AnyConnect application integration page, find the Manage section and select single sign-on.
On the Select a single sign-on method page, select SAML.
On the Set up single sign-on with SAML page, click the edit/pen icon for Basic SAML Configuration to edit the settings.
On the Set up single sign-on with SAML page, enter the values for the following fields:
a. In the Identifier text box, type a URL using the following pattern:
< YOUR CISCO ANYCONNECT VPN VALUE >b. In the Reply URL text box, type a URL using the following pattern:
< YOUR CISCO ANYCONNECT VPN VALUE >Note
These values are not real. Update these values with the actual Identifier and Reply URL. Contact Cisco AnyConnect Client support team to get these values. You can also refer to the patterns shown in the Basic SAML Configuration section in the Azure portal.
On the Set up single sign-on with SAML page, in the SAML Signing Certificate section, find Certificate (Base64) and select Download to download the certificate file and save it on your computer.
On the Set up Cisco AnyConnect section, copy the appropriate URL(s) based on your requirement.
Note
If you would like to on board multiple TGTs of the server then you need to add multiple instance of the Cisco AnyConnect application from the gallery. Also you can choose to upload your own certificate in Azure AD for all these application instances. That way you can have same certificate for the applications but you can configure different Identifier and Reply URL for every application.
Create an Azure AD test user
In this section, you'll create a test user in the Azure portal called B.Simon.
- From the left pane in the Azure portal, select Azure Active Directory, select Users, and then select All users.
- Select New user at the top of the screen.
- In the User properties, follow these steps:
- In the Name field, enter
B.Simon. - In the User name field, enter the username@companydomain.extension. For example,
B.Simon@contoso.com. - Select the Show password check box, and then write down the value that's displayed in the Password box.
- Click Create.
- In the Name field, enter
Assign the Azure AD test user
In this section, you'll enable B.Simon to use Azure single sign-on by granting access to Cisco AnyConnect.
- In the Azure portal, select Enterprise Applications, and then select All applications.
- In the applications list, select Cisco AnyConnect.
- In the app's overview page, find the Manage section and select Users and groups.
- Select Add user, then select Users and groups in the Add Assignment dialog.
- In the Users and groups dialog, select B.Simon from the Users list, then click the Select button at the bottom of the screen.
- If you are expecting a role to be assigned to the users, you can select it from the Select a role dropdown. If no role has been set up for this app, you see 'Default Access' role selected.
- In the Add Assignment dialog, click the Assign button.
Configure Cisco AnyConnect SSO
You are going to do this on the CLI first, you might come back through and do an ASDM walk-through at another time.
Connect to your VPN Appliance, you are going to be using an ASA running 9.8 code train, and your VPN clients will be 4.6+.
First you will create a Trustpoint and import our SAML cert.
The following commands will provision your SAML IdP.
Now you can apply SAML Authentication to a VPN Tunnel Configuration.
Note
There is a feature with the SAML IdP configuration - If you make changes to the IdP config you need to remove the saml identity-provider config from your Tunnel Group and re-apply it for the changes to become effective.
Create Cisco AnyConnect test user
In this section, you create a user called Britta Simon in Cisco AnyConnect. Work with Cisco AnyConnect support team to add the users in the Cisco AnyConnect platform. Users must be created and activated before you use single sign-on.
Test SSO
Anyconnect Ad Authentication Failed
In this section, you test your Azure AD single sign-on configuration with following options.
Anyconnect Ad Authentication App
- Click on Test this application in Azure portal and you should be automatically signed in to the Cisco AnyConnect for which you set up the SSO
- You can use Microsoft Access Panel. When you click the Cisco AnyConnect tile in the Access Panel, you should be automatically signed in to the Cisco AnyConnect for which you set up the SSO. For more information about the Access Panel, see Introduction to the Access Panel.
Next Steps
Anyconnect Ad Authentication Failed
Once you configure Cisco AnyConnect you can enforce session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Cloud App Security.
